HCA Healthcare Data Breach
American health care operator, HCA Healthcare, this week confirmed that they had been targeted by hackers in a large cyberattack. In the ensuing data breach, the personal data of at least 11 million patients were leaked online to hacker forums, where such details can sell for a lot of money. HCA Healthcare is a giant in the medical industry, operating over 180 hospitals in the US and the UK: this is one of the biggest data breaches in health care history.
Who Was Affected and What Was Compromised?
The breach itself occurred on July 5th, and the majority of the 11 million affected patients come from 20 states, including California, Florida, Georgia, and Texas. Compromised data includes:
- Full names
- Home addresses
- Phone numbers
- DOB
- Email addresses
- Gender
- Appointment dates and location

The threat actor initially withheld leaking the data, instead opting to extort HCA. When HCA did not meet demands, the threat actor began posting the now-for-sale data on the forums mentioned above. Investigations are ongoing into precisely what went wrong, with HCA actively cooperating with law enforcement. HCA have stated:
“HCA Healthcare believes that the list contains approximately 27 million rows of data that may include information for approximately 11 million HCA Healthcare patients […] There has been no disruption to the care and services HCA Healthcare provides to patients and communities.”
Protect Your Data
Be sure to follow these three best practices to stay ahead of identity thieves:
- Stay on top of bills: Know what you owe and when it’s due. If you stop receiving a bill, and it wasn’t you that made this change, this could be a red flag that someone has changed your billing address. Similarly, if you receive new bills, which you didn’t sign up for, an identity thieve may be using your personally identifiable information (PII).
- Bank statements: You should regularly review your bank account statements. If you see a transaction that you don’t recognize, it could be a sign that your identity has been stolen.
- Credit report: You should also check your credit regularly. To do so you’ll need to request a report from the three credit-reporting bureaus (Equifax, Experian, and TransUnion). Your credit score isn’t enough to ascertain if you’re identity has been stolen; you’ll need the full report to check for unknown accounts and transactions, and to look for any false information. For a guide on how to do this, head over here!
Further top tips:
- Check your health insurance records and tax return information
- Make sure you always have access to sensitive online accounts
- Watch out for spam emails, texts, and mail
- Check for physical mail and stolen trash
- Always know where your ID, credit cards, and other sensitive documents are kept
- Check your “mySocial Security” account for signs of fraud
Protecting Your Identity and Personal Info
Compromised personal data can have serious consequences, including identity theft, financial fraud, and job losses. The best thing you can do is a) have reliable cybersecurity protection, and b) ensure you will find out ASAP in the event of being affected. We would encourage readers to head over to our new FREE ID Protection platform, which has been designed to meet these challenges.
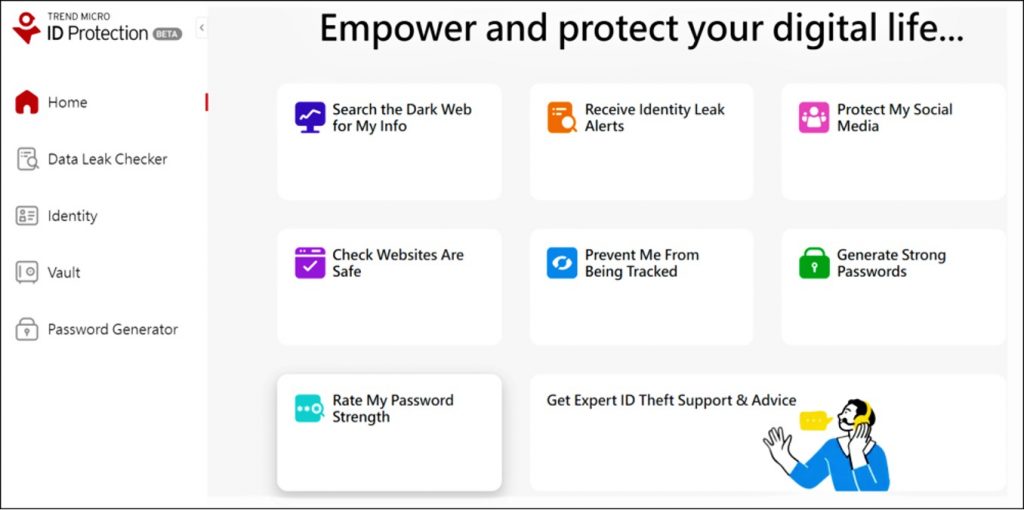
With ID Protection, you can:
- Check to see if your data (email, number, password, credit card) has been exposed in a leak, or is up for grabs on the dark web;
- Secure your social media accounts with our Social Media Account Monitoring tool, with which you’ll receive a personalized report;
- Receive the strongest tough-to-hack password suggestions from our advanced AI (they’ll be safely stored in your Vault);
- Enjoy a safer browsing experience, as Trend Micro checks websites and prevents trackers.
All this for free — why not give it a go today? As always, we hope this article has been an interesting and/or useful read. If so, please do SHARE it with family and friends to help keep the online community secure and informed — and consider leaving a like or comment below. Here’s to a secure 2023!
