T-Mobile Confirms Data Leak Potentially Affecting Over 100 Million Customers (Updated: Aug 2022)
Last Updated on Aug 16, 2022
T-Mobile has agreed to pay $350 million to settle the class-action lawsuit that came as a result of this data breach. Although it hasn’t been finalized, if the settlement goes through, American T-Mobile customers who were affected will be entitled to their share of what will be the second largest settlement in US history.
Details about the payment plan, including how affected customers can claim haven’t been released yet, but eligible class members in lawsuits such as this are usually notified by mail or email.
Be on the Lookout
If you believe that your data may have been compromised in the T-Mobile leak, here are some things to think about:
- Be very suspicious of any requests or alerts (via email, text, or over the phone) relating to something you have no knowledge of. For example, an email stating there was an attempt to log in to one of your online accounts, or somebody asking you to give them access to your computer.
- Correspondence that appears to come from the Social Security Administration, the IRS, or any government agency or financial institution asking you to supply additional information or stating that you owe money.
- Packages showing up on your doorstep that you didn’t order.
We can’t list all the signs of every type of scam cybercriminals may commit using leaked data, so if you believe you may be a victim, please be extra cautious. Also, remember to enable two-factor authentication on all your online accounts for extra security.
T-Mobile Data Leak Explained
T-Mobile has launched an investigation into the data leak that has resulted in the personal information of millions of its customers being posted for sale online.
In a statement released on Monday, the mobile communications giant confirmed that data was “illegally accessed” from its systems, but remained tight-lipped about its nature. However, on a positive note, the company also stated that it is “confident that the entry point used to gain access has been closed.”
It was on an underground forum that a hacker claimed to be in possession of the data. The hacker, named SubVirt, recently posted on the site asking for 6 Bitcoin (a little under $270,000) for a 30-million customer subset of the data, which is purported to include customers’ names, phone numbers, Social Security numbers, driver’s license information, IMEI numbers, and more. SubVirt is alleged to have the personal data of over 100 million T-Mobile customers, however.
Hopefully the authorities will track down SubVirt before the data has a chance to be made public. Unfortunately, this does add to T-Mobile’s recent string of data leaks. It was only back in January that the company admitted that hackers gained access to the call records of over 200,000 of its customers, and in 2018 personal data belonging to around 2 million of its customers was stolen.
What Cybercriminals Are Looking to Do
Leaked data can be used by cybercriminals in many ways:
- Identity theft
- Targeted phishing attacks
- Brute-force attacks to try and gain full access to online accounts
- SIM swap attacks, which allow hackers to get around multi-factor authentication
- Smishing attacks, which are used to trick victims into revealing additional personal information
Use Trend Micro ID Security to find out if your information has been made public. It scans the internet and the dark web, and if your data has been shared online, it will notify you and tell you exactly where it was found.
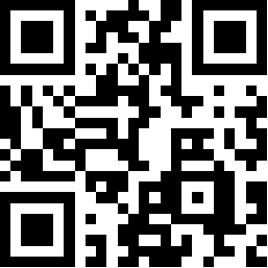
Scan the QR code to download Trend Micro ID Security for Android/iOS now:
Or click the button below:
0 Comments
Other Topics
