Almost immediately after being disclosed publicly, a vulnerability with routers running Arcadyan firmware has been exploited by hackers, potentially affecting millions of home routers.
Although this vulnerability was disclosed to router manufacturers in April, it was made public on August 3. There have been reports of hackers actively attacking these compromised routers since.
What is the issue?
The vulnerability, referred to as CVE-2021-20090, is a critical path traversal vulnerability in the web interfaces of routers with Arcadyan firmware. The vulnerability allows remote attackers to bypass authentication. This makes it possible for attackers to deploy Mirai botnet malicious payloads to affected devices.
Why should I be concerned?
This vulnerability can allow an unauthenticated remote attacker to take control of connected devices. Once this happens, the attacker can:
- Manipulate your internet traffic
- Gain access to sensitive information on your devices
- Alter router settings to make your network more vulnerable
Because not a lot of people are even aware of this security risk and people do not change their routers very frequently, this vulnerability presents a very serious problem for many.
How to check if your router is affected
Here is the list of confirmed devices affected by this vulnerability:
| Manufacturer | Device Model | Affected Firmware Version |
ADB | ADSL wireless IAD router | 1.26S-R-3P |
Arcadyan | ARV7519 | 00.96.00.96.617ES |
Arcadyan | ARV7519 | 00.96.00.96.617ES |
Arcadyan | VRV9517 | 6.00.17 build04 |
Arcadyan | VGV7519 | 3.01.116 |
Arcadyan | VRV9518 | 1.01.00 build44 |
ASMAX | BBR-4MG / SMC7908 ADSL | 0.08 |
ASUS | DSL-AC88U (Arc VRV9517) | 1.10.05 build502 |
ASUS | DSL-AC87VG (Arc VRV9510) | 1.05.18 build305 |
ASUS | DSL-AC3100 | 1.10.05 build503 |
ASUS | DSL-AC68VG | 5.00.08 build272 |
Beeline | Smart Box Flash | 1.00.13_beta4 |
British Telecom | WE410443-SA | 1.02.12 build02 |
Buffalo | WSR-2533DHPL2 | 1.02 |
Buffalo | WSR-2533DHP3 | 1.24 |
Buffalo | BBR-4HG | |
Buffalo | BBR-4MG | 2.08 Release 0002 |
Buffalo | WSR-3200AX4S | 1.1 |
Buffalo | WSR-1166DHP2 | 1.15 |
Buffalo | WXR-5700AX7S | 1.11 |
Deutsche Telekom | Speedport Smart 3 | 010137.4.8.001.0 |
HughesNet | HT2000W | 0.10.10 |
KPN | ExperiaBox V10A (Arcadyan VRV9517) | 5.00.48 build453 |
KPN | VGV7519 | 3.01.116 |
O2 | HomeBox 6441 | 1.01.36 |
Orange | LiveBox Fibra (PRV3399) | 00.96.00.96.617ES |
Skinny | Smart Modem (Arcadyan VRV9517) | 6.00.16 build01 |
SparkNZ | Smart Modem (Arcadyan VRV9517) | 6.00.17 build04 |
Telecom (Argentina) | Arcadyan VRV9518VAC23-A-OS-AM | 1.01.00 build44 |
TelMex | PRV33AC | 1.31.005.0012 |
TelMex | VRV7006 | |
Telstra | Smart Modem Gen 2 (LH1000) | 0.13.01r |
Telus | WiFi Hub (PRV65B444A-S-TS) | v3.00.20 |
Telus | NH20A | 1.00.10debug build06 |
Verizon | Fios G3100 | 2.0.0.6 |
Vodafone | EasyBox 904 | 4.16 |
Vodafone | EasyBox 903 | 30.05.714 |
Vodafone | EasyBox 802 | 20.02.226 |
For more information, visit Tenable.
Secure Your Wi-Fi Router and Protect Your Home Network
Affected users should contact their respective vendors for update information and support. Ideally, a resolution will be available for all soon. However, this won’t stop hackers and threat actors from forever seeking new ways to compromise people’s security. To ensure your home network stays protected use Trend Micro Home Network Security.
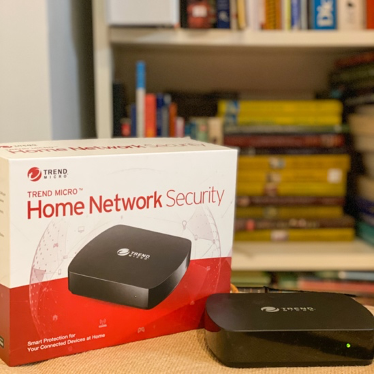
The Home Network Security station is a device that connects to your home Wi-Fi router with an Ethernet cable. Once setup is complete, the station scans all traffic passing in and out of your home network, allowing it to prevent intrusions, block hacking attempts and web threats as well as protect your family’s privacy.
Home Network Security provides your home network with an essential extra layer of protection. Click the button below to learn more:
0 Comments
Other Topics
